Reliably compliant – IT security that pays off

In order to remain competitive as a company, it is vital to respond quickly to new technologies and new business models. Flexibly adaptable IT environments significantly simplify and accelerate these processes. IT security is an important factor in growth and change processes.
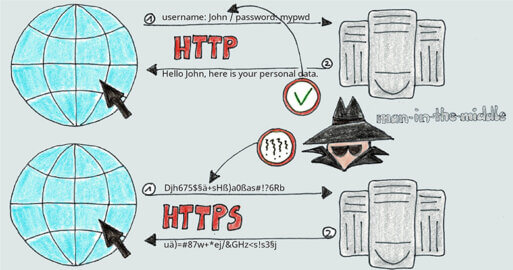
Data Transfer – Security Gap Number One Concern
A recent IBM Study found the average damage caused to a company per data breach amounts to 3.9 Million US Dollars. Financial penalties imposed for non-compliance with certain regulations, General Data Protection Regulation (GDPR) for example, can reach far higher.
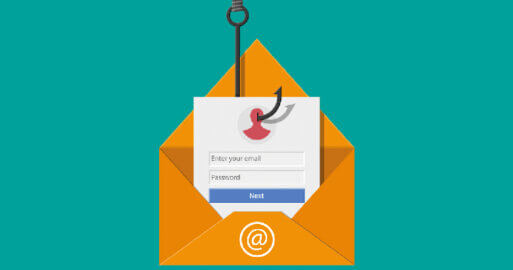
According to an IDC study on the development of the Global DataSphere published in November 2018, the annual volume of global data produced will more than quintuple over the next six years. The requirement to securely exchange that data (particularly sensitive data) is also increasing. precisesecurity.com states that in 2019 as many as 75% of German companies were affected by IT security incidents, with damage amounting to €102.9 billion. The most common cybercrimes were password attacks, malware infection and phishing. The main focus of cyber criminals was on communications and financial data. Data in transit represents the greatest potential danger. The unencrypted transmission of data via email or outdated FTP connections offers a wide-open gateway and is the main point of attack for data theft.
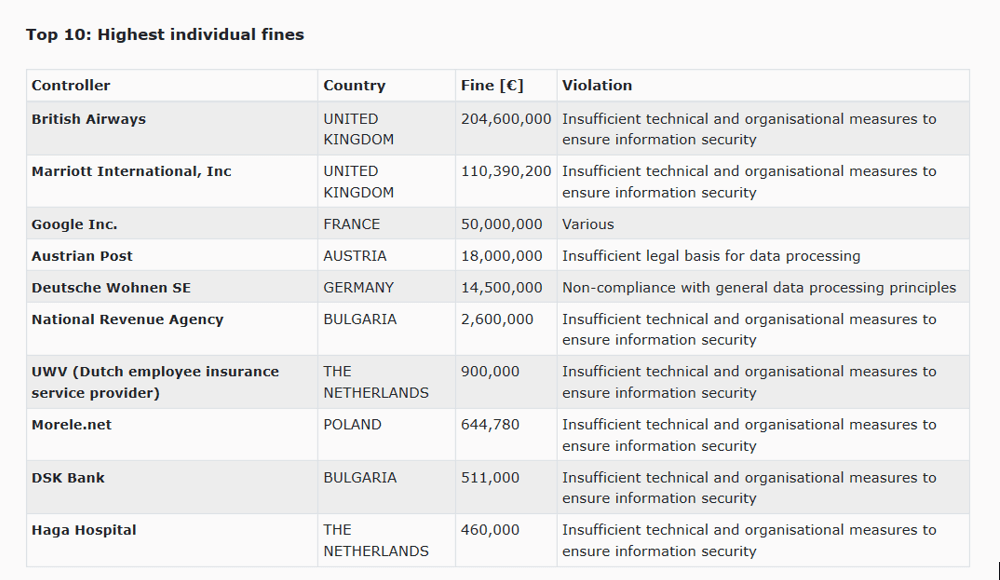
Non-Compliance – Violations of the GDPR guidelines are punished with high fines
In May 2018, GDPR was introduced in an effort to protect Personally Identifiable Information (PII). Looking at the level of fines that EU companies had to pay in 2018 for breaches of data protection directives (see below), it becomes clear as to how rewarding a review of in-house IT systems and the extent to which all regulatory requirements are reliably met can be:
Automation and the secure and efficient design of IT processes are therefore often at the top of the digital agenda for many companies.
SEEBURGEER BIS Managed File Transfer-Solution
Security for all types of data transfer
SEEBURGER AG has developed the BIS MFT solution to support companies in the secure exchange of data. The coordination of company-wide data streams requires security, control and transparency. SEEBURGER’s MFT solution comprehensively ensures this via two core building blocks: the MFT Gateway ensures the secure transfer of data and the MFT Management ensures efficient administration and control. Whether automated or ad-hoc, the BIS MFT solution delivers security, transparency and traceability for your file transfers.
Advantages:
Demonstrate Compliance – Adhering to changes such as GDPR without an appropriate IT solution in place cannot only prove to be challenging, but also costly in the case of incurred penalties. These regulatory rules are challenging to implement, especially in a sprawling IT landscape that never seems to stay static. With an MFT solution in place, regulatory rules can be reflected in the workflow and centrally managed to easily accommodate future changes.
Control Intellectual Property (IP) – After its people, a company’s most prized asset is its intellectual property (IP). Without an appropriate IT solution in place, leakage of IP can cause potential harm on multiple inextricably linked fronts, e.g. loss of competitive advantage, financial penalties incurred for negligence, share value depreciation, brand trust issues amongst the markets etc. Such risks are vastly mitigated by a MFT solution in place.
Conclusion:
Focus on Core Business – The most successful companies are those that are able to execute against their plan / vision without being sucked into the vacuum of non-core business activity, e.g. figuring out how to move computer files around that contain sensitive/important data (often large in size). Without an appropriate IT solution in place, staff wastes valuable time in trying to manipulate outdated tools and inappropriate practices trying to get their core job done. With an MFT solution in place, employees and machines are empowered to send files containing sensitive data to the right place at the right time, all with maximum efficiency and with the minimum of fuss.
Isn’t it odd that companies often don’t provide the budget for a security initiative, but are willing to spend almost anything to recover the damage caused by a rule violation?
Thank you for your message
We appreciate your interest in SEEBURGER
Get in contact with us:
Please enter details about your project in the message section so we can direct your inquiry to the right consultant.
Written by: Christoph Stäb
Christoph Staeb is the Corporate Information Security Officer (CISO) at SEEBURGER. He has 14 years of experience with the quality management and security considerations of SEEBURGER products and services. He has achieved ISO/IEC 27001 and ISAE 3402 (SOC 1) Type 2 certifications for SEEBURGER Cloud Services and knows the insides of data center operation in compliance with guidelines in international environments.