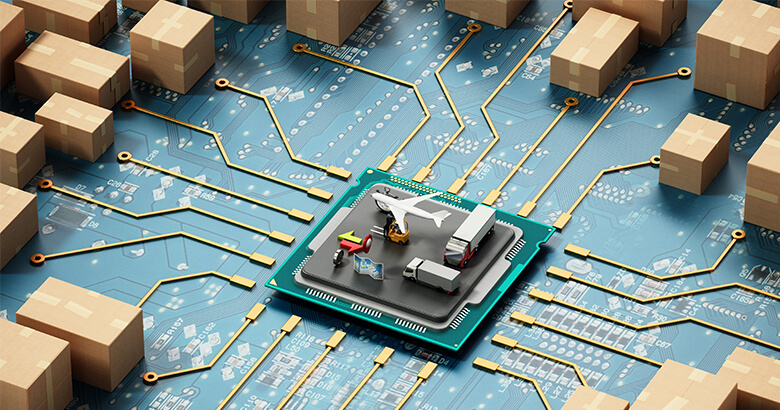
Is a Digital Goods Receipt Process a Nice Extra or a Necessity in Supply Chain Management?
| Alex Jende | Reading Time: 5 min
Is a digital goods receipt process a nice extra or a necessity in supply chain management (SCM)? When it comes to modernizing a receipt of goods process, including the incoming goods inspection and quality control, people talk a lot about digitalization. However, to what degree does digitalization actually have an impact on improving logistics processes […]