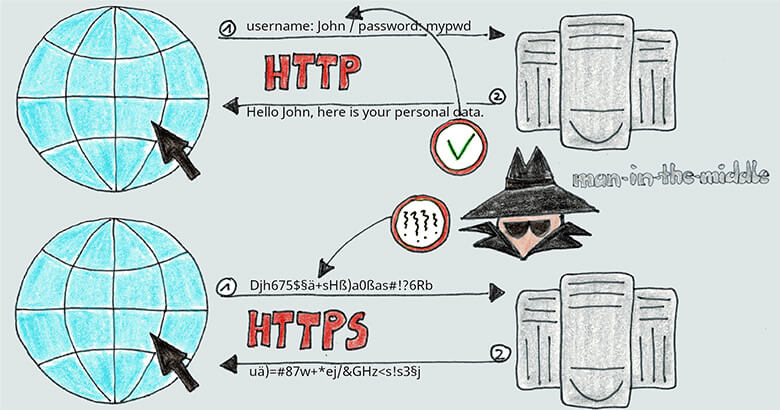
Three Steps to Greater Data Security by Improving Your TLS Encryption
| Ramona Becker | Reading Time: 7 min
The worlds of digital security and data transmission do not stand still, which is why it’s important to keep evolving your encryption protocols. Our SEEBURGER Cloud Services, which process a wealth of sensitive information, are continually updated to ensure they meet the highest security standards. In this article, we’ll be taking a look at the […]